
Don’t be a Victim of Facebook Cloning
February 7, 2017
What is the Cloud and How does it Work?
February 13, 2017No not “fishing” the leisurely activity with a hook and pole. Unfortunately, “phishing” isn’t nearly as relaxing or enjoyable. So, what is phishing? An email that is fake and designed to steal information about you, such as usernames and passwords.
When you click on a link in a “phishing” email, it takes you to a website that is hacker territory. This fake page is often made to look like something you are familiar with, say the login for Wells Fargo, Chase Manhattan Bank or Google Drive. But, it is a copy of the page.
The danger arises when you fill in the blanks on the fake page. If it contains a place for you to put your Username and Password, that data goes to the bad guys.
Email phishing scams are nothing new. What’s different is how tricky the emails are becoming, and the numbers of people sucked into clicking on them. The latest Gmail phishing scam is so sophisticated that even the “experts” are getting fooled.
The Latest Gmail Phishing Hack
In the latest Gmail Phishing hack, the email comes from someone you know and the subject line may have been used before, so it looks familiar. The attachment is a picture of an attachment that contains a link, and it asks you to “log in” to access the attachment. The login screen URL is not green at the top with a padlock and a “https://” address, but instead, contains a “data:text/html,https://accounts.google.com/ServiceLogin?” address.
So, how do you know if an email is a phishing scam? There are obvious clues that an email might be a phishing scam, as well as some not so obvious ones. The best advice I can give is to keep yourself educated on how to recognize fake email.
Not so subtle clues you being phished:
- It’s from a company you do not do business with claiming your account needs attention. (Chase Manhattan bank tells you they need information from you)
- It’s from your email provider telling you your email isn’t working (um, hello, you just received this and a ton of other emails with no problems)
- You receive an email from a stranger asking you to download a file or click on a link.
- An email about an existing account comes from a sender with a non-related email address. (Email tells you there is a problem with your Wells Fargo account and they have an AOL email address.)
Subtle and harder to recognize clues:
- Someone you know sends a random link. Never click on a strange link, especially if you have not been speaking to the sender and the email is out of context.
- Someone you know sends an attachment asking you to look it over.
Below is a photo of an email sent to me at my law office. It is from a law firm my partner has dealt with, but not me. Here are some clues that this isn’t a legit email.
- The name of the document is not professional.
- The sender’s email address is a Gmail address, not one associated with this law firm.
- It is not an expected email regarding an existing case or matter in the office.
- The attachment is strange and requests that I click on a link.
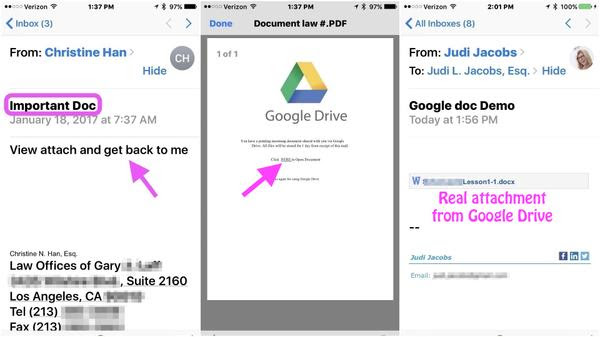
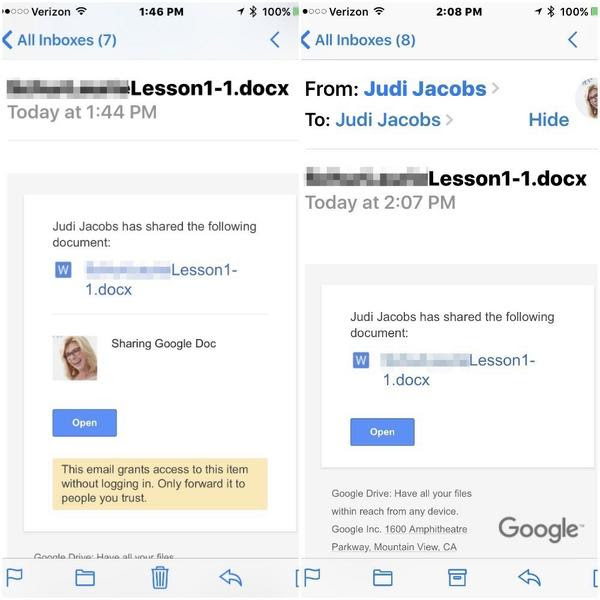
The image below shows how a real Google doc attachment appears.
How do you keep yourself safe from email phishing scams?
If it looks strange, delete the email! For every login page, verify the presence of the green padlock and “https” in the address.
I can’t emphasize enough the need to create complex passwords. A password comprised of letters and numbers that make up a word in the English language won’t cut it.
If you suspect a friend’s account has been hacked, do not email them. Call or text them to advise or ask if they know what they just sent to you. Then make sure you mark spam in your email as spam (don’t just delete it).
The Latest Autofill Hack through Phishing
A newly discovered browser weakness comes through an email—and the result is that the bad guys get access to information stored in Autofill in your Chrome, Opera, or Safari browsers or, those using the LastPass browser autofill extension.
It starts with an email that says “click here” to buy something, and you fall for it. The best protection is to turn off the Autofill features of your browsers. It will 100% prevent the access to your data from this type of email. If you are very careful with your email and astute at recognizing threats, you can keep using Autofill features.
Here are step-by-step instructions for turning off autofill on your computers and phones.
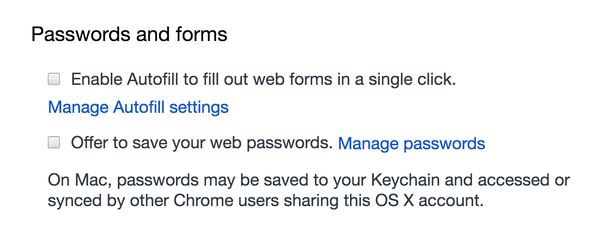
Chrome autofill access:
• Preferences > Settings > advanced settings > Passwords and forms
• Uncheck the boxes as shown below to turn off Autofill
Chrome autofill access on the iPhone:
- Three parallel dots in upper right corner > Settings > Autofill forms
- Toggle off/on as desired for Autofill & addresses and credit cards.
Safari autofill access:
- Safari > Preferences (from the menu under Safari) > Passwords
- Uncheck the box as shown to turn off Autofill

Safari autofill settings on the iPhone
- Safari > Autofill
- Turn off or on by toggling off/on “Use Contact Info.”
- Turn off or Names and Passwords or Credit Cards
- (All info stored in Keychain vault of iCloud which is encrypted)
Another way to protect yourself is to keep your browser up to date. An updated browser gets the security patches and improvements to ensure prevention against the latest threats.
Educate yourself on how to recognize these phishing schemes. Remember, knowledge is power.






